-
Designing a Hipaa-Compliant Security Operations CenterA Guide to Detecting and Responding
Apress 出版Develop a comprehensive plan for building a HIPAA-compliant security operations center, designed to
-
E-Mail Klassifizierung in einem CRM-System anhand von Text Mining Analyseverfahren
Ingram 出版Bachelorarbeit aus dem Jahr 2019 im Fachbereich Informatik - Internet, neue Technologien, Note: 1,0
-
Criptomoneda
Ingram 出版Un recurso sin prejuicios para comenzar su viaje Crypto, de cero a h矇roe!En este libro aprender獺s:
-
-
Criptomonedas
Ingram 出版Las ganancias supranormales que se obtienen en el mercado de la criptomoneda han llamado la atenci籀
-
Criptomoneda
Ingram 出版Hay muchas gu穩as en el mercado que tratan acerca del presente t籀pico, 癒gracias de nuevo por haber e
-
Criptomoneda
Ingram 出版A partir de lo b獺sico, paso a explicar todo lo que necesita saber para decidirse por el potencial,
-
-
Criptomoneda
Ingram 出版Para aquellos que se comprometen al aprendizaje del arte del trading de criptomonedas, nunca volver
-
Tribe of Hackers Security Leaders
Ingram 出版Tribal Knowledge from the Best in Cybersecurity Leadership The Tribe of Hackers series continues, s
-
-
Artificial Intelligence
Ingram 出版If you want to learn about artificial intelligence without having to go through a boring textbook,
-
Inteligencia Artificial
Ingram 出版2 manuscritos completos en 1 libro Inteligencia artificial: Lo que usted necesita saber sobre el a
-
Artificial Intelligence
Ingram 出版If you want to learn about artificial intelligence without having to go through a boring textbook,
-
Cybersecurity For Beginners
Ingram 出版If you want to protect yourself and your family from the increasing risk of cyber-attacks, then kee
-
Smarter World, Bigger Threats
Ingram 出版The information technology revolution has significantly changed the way in which people interact wi
-
Criptomoneda
Ingram 出版Para aquellos que se comprometen al aprendizaje del arte del trading de criptomonedas, nunca volver
-
Hacking For Beginners
Ingram 出版Do you want to keep your personal data safe from prying eyes? Do you want to look behind the scenes
-
Inteligencia Artificial
Ingram 出版2 manuscritos completos en 1 libro Inteligencia artificial: Lo que usted necesita saber sobre el a
-
Smarter World, Bigger Threats
Ingram 出版The information technology revolution has significantly changed the way in which people interact wi
-
Darknet Secrets
Ingram 出版If You Want To Take Back Your Right To Privacy in 2019, Then Keep Reading... Do you want to surf th
-
Blogging 2020
Ingram 出版If you want to discover how to make a blog that can provide you with passive income, then keep read
-
-
-
-
The Temple of Django Database Performance
Ingram 出版Most performance problems in web applications come down to one thing: the database.With Django, the
-
Implementing an Information Security Management System
Apress 出版Covers security standards based on ISO 27001Includes best practices on Audits and AssessmentsFollow
-
Angular for Material Design
Apress 出版Build Angular applications faster and better with TypeScript and Material Design. You will learn ho
-
-
Learning Bulma
Apress 出版Learn to use Bulma in your HTML file by applying easy-to-understand practical examples to create re
-
Operation Espionage
Ingram 出版Insider threat is a real issue, pain point, and can be a challenge in any organization of any size
-
-
Mastering C# (C Sharp Programming)
Ingram 出版Let's be very honest, a programming language cannot be learned in "one day" or "fast". You will nee
-
Bug Bounty Hunting for Web Security
Apress 出版Includes Sender Policy Framework testing and exploitationCovers Header Injection and URL Redirectio
-
-
-
-
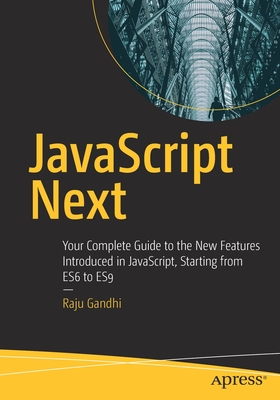
JavaScript Next
Apress 出版JavaScript has finally grown up. Armed with a slew of new features, JavaScript now makes writing th
-
-
Computer Networking
Ingram 出版Keeping this high-demand information from yourself will be detrimental to your technologically-clue
-
Programming Pytorch for Deep Learning
Oreilly & 出版Take the next steps toward mastering deep learning, the machine learning method that璽 s transformin
-
-
-
-
-
Cyber Security
Ingram 出版Want to Keep Your Devices and Networks Safe from Cyberattacks with Just a Few Easy Steps? Read on.
-
-
熱門搜尋
搜尋:安全混币器 ,全館搜尋共計9563筆,頁數114/200
- 篩選
-
排序
- 圖片式
- 條列式
-
館別
-
大分類
-
購買狀態
-
作者
-
出版社
-
品牌
-
商品規格
-
出版日期
-
價格區間
-
運送方式