Complexity = Corruption Big Tech 5
The Big Tech 5 are like one giant octopus, with tentacles invading every aspect of our lives. Octopus tentacles are mostly benign, even helpful, but there is always the fear of a venomous bite or being enveloped in a pool of black ink so dense we can no longer see. Why is this pool of black ink so scary? It obfuscates my moral compass and is literally overwhelming. The Big Tech 5 and the Land of the Internet and my ebooks series, COMPLEXITY = CORRUPTION, are based on my experience and knowledge. As an activist author, I always advocate for change. The framework for this volume is Facebook.
Network and System Security
This book constitutes the refereed proceedings of the 15th International Conference on Network and System Security, NSS 2021, held in Tianjin, China, on October 23, 2021. The 16 full and 8 short papers presented in this book were carefully reviewed and selected from 62 submissions. They focus on theoretical and practical aspects of network and system security, such as authentication, access control, availability, integrity, privacy, confidentiality, dependability and sustainability of computer networks and systems.
Cybersecurity Leadership Demystified
Gain useful insights into cybersecurity leadership in a modern-day organization with the help of use casesKey Features: Discover tips and expert advice from the leading CISO and author of many cybersecurity booksBecome well-versed with a CISO's day-to-day responsibilities and learn how to perform them with easeUnderstand real-world challenges faced by a CISO and find out the best way to solve themBook Description: The chief information security officer (CISO) is responsible for an organization's information and data security. The CISO's role is challenging as it demands a solid technical foundation as well as effective communication skills. This book is for busy cybersecurity leaders and executives looking to gain deep insights into the domains important for becoming a competent cybersecurity leader.The book begins by introducing you to the CISO's role, where you'll learn key definitions, explore the responsibilities involved, and understand how you can become an efficient CISO. You'll then be taken through end-to-end security operations and compliance standards to help you get to grips with the security landscape. In order to be a good leader, you'll need a good team. This book guides you in building your dream team by familiarizing you with HR management, documentation, and stakeholder onboarding. Despite taking all that care, you might still fall prey to cyber attacks; this book will show you how to quickly respond to an incident to help your organization minimize losses, decrease vulnerabilities, and rebuild services and processes. Finally, you'll explore other key CISO skills that'll help you communicate at both senior and operational levels.By the end of this book, you'll have gained a complete understanding of the CISO's role and be ready to advance your career.What You Will Learn: Understand the key requirements to become a successful CISOExplore the cybersecurity landscape and get to grips with end-to-end security operationsAssimilate compliance standards, governance, and security frameworksFind out how to hire the right talent and manage hiring procedures and budgetDocument the approaches and processes for HR, compliance, and related domainsFamiliarize yourself with incident response, disaster recovery, and business continuityGet the hang of tasks and skills other than hardcore security operationsWho this book is for: This book is for aspiring as well as existing CISOs. This book will also help cybersecurity leaders and security professionals understand leadership in this domain and motivate them to become leaders. A clear understanding of cybersecurity posture and a few years of experience as a cybersecurity professional will help you to get the most out of this book.
Encyclopedia of Crash Dump Analysis Patterns, Volume 2, L-Z
This reference reprints with corrections, additional comments, and classification more than 370 alphabetically arranged and cross-referenced memory analysis patterns originally published in Memory Dump Analysis Anthology volumes 1 - 13. This pattern catalog is a part of pattern-oriented software diagnostics, forensics, prognostics, root cause analysis, and debugging developed by Software Diagnostics Institute. Most of the analysis patterns are illustrated with examples for WinDbg from Debugging Tools for Windows with a few examples from Mac OS X and Linux for GDB. The third edition includes more than 40 new analysis patterns, more than 30 new examples and comments for analysis patterns published in the previous editions, updated bibliography and links, improved illustrations, and debugger output snippets with extra visual highlighting. Volume 2 contains L-Z encyclopedia entries, bibliography, appendixes, and the index.
The Cybersecurity Mindset
Securing an organization's assets and understanding the cybersecurity blueprint goes beyond the technical scope. Hackers are sharing information and gaining an informational advantage. It's time to modernize our defensive tactics and deploy a "Cybersecurity Mindset."The Cybersecurity Mindset: A Virtual and Transformational Thinking Mode is a first-ever coverage of the mental engagement and proactive strategies required to secure business assets and technologies; and can further serve as a resource guide or playbook. The Cybersecurity Mindset provides a layered approach to thinking holistically about cybersecurity and engineering protection standards for data, applications, information, and cloud services. The information discussed in The Cybersecurity Mindset is transferrable for technology and non-technology professionals involved with the security industry, and it provides application-based knowledge to further certification or academic requirements.
Memory Dump Analysis Anthology, Volume 5, Revised Edition
This reference volume consists of revised, edited, cross-referenced, and thematically organized articles from Software Diagnostics Institute and Software Diagnostics Library (former Crash Dump Analysis blog) written in February 2010 - October 2010. In addition to various corrections, this major revision updates relevant links and removes obsolete references. Some articles are preserved for historical reasons. Most of the content, especially memory analysis and trace and log analysis pattern languages, is still relevant today and for the foreseeable future. Crash dump analysis pattern names are also corrected to reflect the continued expansion of the catalog. The fifth volume features: - 25 new crash dump analysis patterns; - 11 new pattern interaction case studies (including software tracing); - 16 new trace analysis patterns; - 7 structural memory patterns; - 4 modeling case studies for memory dump analysis patterns; - Discussion of 3 common analysis mistakes; - Malware analysis case study; - Computer independent architecture of crash analysis report service; - Expanded coverage of software narratology; - Metaphysical and theological implications of memory dump worldview; - More pictures of memory space and physicalist art; - Classification of memory visualization tools; - Memory visualization case studies; - Close reading of the stories of Sherlock Holmes: Dr. Watson's observational patterns; - Fully cross-referenced with Volumes 1 - 4.The primary audience for Memory Dump Analysis Anthology reference volumes is: software engineers developing and maintaining products on Windows platforms, technical support, escalation, and site reliability engineers dealing with complex software issues, quality assurance engineers testing software on Windows platforms, security and vulnerability researchers, reverse engineers, malware and memory forensics analysts. Trace and log analysis articles may be of interest to users of other platforms.
The Cybersecurity Mindset
Securing an organization's assets and understanding the cybersecurity blueprint goes beyond the technical scope. Hackers are sharing information and gaining an informational advantage. It's time to modernize our defensive tactics and deploy a "Cybersecurity Mindset."The Cybersecurity Mindset: A Virtual and Transformational Thinking Mode is a first-ever coverage of the mental engagement and proactive strategies required to secure business assets and technologies; and can further serve as a resource guide or playbook. The Cybersecurity Mindset provides a layered approach to thinking holistically about cybersecurity and engineering protection standards for data, applications, information, and cloud services. The information discussed in The Cybersecurity Mindset is transferrable for technology and non-technology professionals involved with the security industry, and it provides application-based knowledge to further certification or academic requirements.
PocketFocus Notebook
PocketFocus Notebooks are single-project notebooks for designers, marketers, artists, project managers, and any one else that likes to keep things organized, one project at a time. The PocketFocus is a stylish, modern, 36-page notebook has an open space on the cover for clean labeling without branding, while still being minimalist and chic. There are enough pages to think, plan, note, and design - but not so many you waste half of a notebook. The pocket-size makes it easy for you to carry and store as many as you need.
Navigating Hyperspace
Like a hurricane that exposes the underlying bedrock--and an occasional hidden treasure--by washing away the accumulated grains of sand, the pandemic blew away the accumulated certainties and securities of the globally connected, digitized society. Suddenly, nothing can be taken for granted: visiting ailing relatives, shopping--or going to church. The internet and, particularly, social networking sites have become the indispensable infrastructure holding our sociability together. The global companies of the digital economy profited handsomely. How about the users of their services? This volume explores how priests inhabit the digital environment of social networking sites, specifically Facebook. The authors looked at how they present themselves, what they publish, and how people engage with this content. The context of the pandemic suggested that we should also examine how digital technology and social media are being used for purposes of priestly ministry. Our hope is that these analyses and considerations will help not just priests but every person at becoming proficient not only in things virtual but also in practicing virtue.
KI 2021: Advances in Artificial Intelligence
This book constitutes the refereed proceedings of the 44th German Conference on Artificial Intelligence, KI 2021, held in September/October 2021. Due to COVID-19 pandemic the conference was held virtually. The 16 full and 4 short papers with one extended abstract were carefully reviewed and selected from 59 submissions. As well-established annual conference series KI is dedicated to research on theory and applications across all methods and topic areas of AI research.
Mediated Interfaces
Images of faces, bodies, selves and digital subjectivities abound on new media platforms like Snapchat, Instagram, YouTube, and others-these images represent our new way of being online and of becoming socially mediated. Although researchers are examining digital embodiment, digital representations, and visual vernaculars as a mode of identity performance and management online, there exists no cohesive collection that compiles all these contemporary philosophies into one reader for use in graduate level classrooms or for scholars studying the field. The rationale for this book is to produce a scholarly fulcrum that pulls together scholars from disparate fields of inquiry in the humanities doing work on the common theme of the socially mediated body. The chapters in Mediated Interfaces: The Body on Social Media represent a diverse list of contributors in terms of author representation, inclusivity of theoretical frameworks of analysis, and geographic reach of empirical work. Divided into three sections representing three dominant paradigms on the socially mediated body: representation, presentation, and embodiment, the book provides classic, creative, and contemporary reworkings of these paradigms.
Critical Information Infrastructures Security
This book constitutes the refereed proceedings of the 16th International Conference on Critical Information Infrastructures Security, CRITIS 2021, which took place in Lausanne, Switzerland, during September 27-29, 2021.The 12 full papers included in this volume were carefully reviewed and selected from 42 submissions. They were organized in topical sections as follows: protection of cyber-physical systems and industrial control systems (ICS); C(I)IP organization, (strategic) management and legal aspects; human factor, security awareness and crisis management for C(I)IP and critical services; and future, TechWatch and forecast for C(I)IP and critical services.
Communication, Networks and Computing
This book constitutes selected and revised papers presented at the Second International Conference on Communication, Networks and Computing, CNC 2020, held in Gwalior, India, in December 2020. The 23 full papers and 7 short papers were thoroughly reviewed and selected from the 102 submissions. They are organized in topical sections on wired and wireless communication systems; high dimensional data representation and processing; networking and information security; computing Techniques for efficient networks design; vehicular technology and application; electronics circuit for communication system.
Redesigning Wiretapping
This book tells the story of government-sponsored wiretapping in Britain and the United States from the rise of telephony in the 1870s until the terrorist attacks of 9/11.It pays particular attention to the 1990s, which marked one of the most dramatic turns in the history of telecommunications interception. During that time, fiber optic and satellite networks rapidly replaced the copper-based analogue telephone system that had remained virtually unchanged since the 1870s. That remarkable technological advance facilitated the rise of the networked home computer, cellular telephony, and the Internet, and users hailed the dawn of the digital information age. However, security agencies such as the FBI and MI5 were concerned. Since the emergence of telegraphy in the 1830s, security services could intercept private messages using wiretaps, and this was facilitated by some of the world's largest telecommunications monopolies such as AT&T in the US and British Telecom in the UK. Thenew, digital networks were incompatible with traditional wiretap technology. To make things more complicated for the security services, these monopolies had been privatized and broken up into smaller companies during the 1980s, and in the new deregulated landscape the agencies had to seek assistance from thousands of startup companies that were often unwilling to help. So for the first time in history, technological and institutional changes posed a threat to the security services' wiretapping activities, and government officials in Washington and London acted quickly to protect their ability to spy, they sought to force the industry to change the very architecture of the digital telecommunications network.This book describes in detail the tense negotiations between governments, the telecommunications industry, and civil liberties groups during an unprecedented moment in history when the above security agencies were unable to wiretap. It reveals for the first time the thoughts of some of the protagonists in these crucial negotiations, and explains why their outcome may have forever altered the trajectory of our information society.
Cryptography and Coding
This book constitutes the refereed proceedings of the 18th IMA International Conference on Cryptography and Coding, IMACC 2021, held in December 2021. Due to COVID 19 pandemic the conference was held virtually. The 14 papers presented were carefully reviewed and selected from 30 submissions. The conference focuses on a diverse set of topics both in cryptography and coding theory.
Incremental Construction of Code Property Graphs
Master's Thesis from the year 2021 in the subject Computer Science - IT-Security, grade: 2,0, Technical University of Munich (Department of Informatics), language: English, abstract: This thesis extends a modified CPG approach that is able to operate on multiple programming languages, i.e. C/C++, Java, Python and Golang, available on GitHub3 [Fra21a]. Graph-based code analysis systems are versatile tools for reasoning about the correctness of complex software projects. One area in which they are widely used is in source code auditing: Security vulnerabilities, for example using cryptographic functions with insecure algorithms, can be introduced by coding patterns that spread over the boundaries of several methods, classes or even files in the project. This is where graph-based analysis makes finding these vulnerabilities easier, by creating a framework where the source code can be represented as a graph and vulnerable
Advanced Smart Computing Technologies in Cybersecurity and Forensics
This book addresses the topics related to artificial intelligence, internet of things, blockchain technology, and machine learning and bring together researchers, developers, practitioners, and users who are interested in cybersecurity and forensics.
Access, Resource Sharing and Collection Development
This book, first published in 1996, explores the role of libraries in acquiring, storing, and disseminating information in different formats to make better use of technology in sharing scarce resources and connecting library users with collections.
Agile Security Operations
Get to grips with security operations through incident response, the ATT&CK framework, active defense, and agile threat intelligenceKey Features: Explore robust and predictable security operations based on measurable service performanceLearn how to improve the security posture and work on security auditsDiscover ways to integrate agile security operations into development and operationsBook Description: Agile security operations allow organizations to survive cybersecurity incidents, deliver key insights into the security posture of an organization, and operate security as an integral part of development and operations. It is, deep down, how security has always operated at its best.Agile Security Operations will teach you how to implement and operate an agile security operations model in your organization. The book focuses on the culture, staffing, technology, strategy, and tactical aspects of security operations. You'll learn how to establish and build a team and transform your existing team into one that can execute agile security operations. As you progress through the chapters, you'll be able to improve your understanding of some of the key concepts of security, align operations with the rest of the business, streamline your operations, learn how to report to senior levels in the organization, and acquire funding.By the end of this Agile book, you'll be ready to start implementing agile security operations, using the book as a handy reference.What You Will Learn: Get acquainted with the changing landscape of security operationsUnderstand how to sense an attacker's motives and capabilitiesGrasp key concepts of the kill chain, the ATT&CK framework, and the Cynefin frameworkGet to grips with designing and developing a defensible security architectureExplore detection and response engineeringOvercome challenges in measuring the security postureDerive and communicate business values through security operationsDiscover ways to implement security as part of development and business operationsWho this book is for: This book is for new and established CSOC managers as well as CISO, CDO, and CIO-level decision-makers. If you work as a cybersecurity engineer or analyst, you'll find this book useful. Intermediate-level knowledge of incident response, cybersecurity, and threat intelligence is necessary to get started with the book.
Phishing and Communication Channels
Mitigate the dangers posed by phishing activities, a common cybercrime carried out through email attacks. This book details tools and techniques to protect against phishing in various communication channels. The aim of phishing is to fraudulently obtain sensitive credentials such as passwords, usernames, or social security numbers by impersonating a trustworthy entity in a digital communication. Phishing attacks have increased exponentially in recent years, and target all categories of web users, leading to huge financial losses to consumers and businesses. According to Verizon's 2020 Data Breach Investigations Report (DBIR), 22% of all breaches in 2019 involved phishing. And 65% of organizations in the USA experience a successful phishing attack. This book discusses the various forms of phishing attacks, the communications most often used to carry out attacks, the devices used in the attacks, and the methods used to protect individuals and organizations fromphishing attacks.What You Will Learn Understand various forms of phishing attacks, including deceptive, DNS-based, search engine, and contents injection phishingKnow which communications are most commonly used, including email, SMS, voice, blog, wifi, and moreBe familiar with phishing kits (what they are) and how security experts utilize them to improve user awarenessBe aware of the techniques that attackers most commonly use to request informationMaster the best solutions (including educational, legal, technical) to protect against phishing attacks Who This Book Is For Security professionals who need to educate online users, especially those who deal with banks, online stores, payment systems, governments organizations, social networks and blogs, IT companies, telecommunications companies, and others. Thesecondary audience includes researchers working to develop novel strategies to fight against phishing activities and undergraduate and graduate instructors of cybersecurity.
Critical Infrastructure Protection XIV
The information infrastructure - comprising computers, embedded devices, networks and software systems - is vital to operations in every sector: chemicals, commercial facilities, communications, critical manufacturing, dams, defense industrial base, emergency services, energy, financial services, food and agriculture, government facilities, healthcare and public health, information technology, nuclear reactors, materials and waste, transportation systems, and water and wastewater systems. Global business and industry, governments, indeed society itself, cannot function if major components of the critical information infrastructure are degraded, disabled or destroyed.Critical Infrastructure Protection XIV describes original research results and innovative applications in the interdisciplinary field of critical infrastructure protection. Also, it highlights the importance of weaving science, technology and policy in crafting sophisticated, yet practical, solutions that will help secure information, computer and network assets in the various critical infrastructure sectors. Areas of coverage include: Aviation Infrastructure Security; Vehicle Infrastructure Security; Telecommunications Systems Security; Industrial Control Systems Security; Cyber-Physical Systems Security; and Infrastructure Modeling and Simulation. This book is the fourteenth volume in the annual series produced by the International Federation for Information Processing (IFIP) Working Group 11.10 on Critical Infrastructure Protection, an international community of scientists, engineers, practitioners and policy makers dedicated to advancing research, development and implementation efforts focused on infrastructure protection. The book contains a selection of sixteen edited papers from the Fourteenth Annual IFIP WG 11.10 International Conference on Critical Infrastructure Protection, held at SRI International, Arlington, Virginia, USA in the spring of 2020. Critical Infrastructure Protection XIV is an important resource for researchers, faculty members and graduate students, as well as for policy makers, practitioners and other individuals with interests in homeland security.
e-Learning in Medical Physics and Engineering
This practical guide provides educators, programme administrators, and school directors with step-by-step instructions on how to best implement the learning mangament system Moodle, focusing on the specific requirements of the education and training of Medical Physics and Engineering students.
Progress in Cryptology - Indocrypt 2021
This book constitutes the refereed proceedings of the 22nd International Conference on Cryptology in India, INDOCRYPT 2021, which was held in Jaipur, India, during December 12-15, 2021.The 27 full papers included in these proceedings were carefully reviewed and selected from 65 submissions. They were organized in topical sections as follows: authenticated encryption; symmetric cryptography; lightweight cryptography; side-channel attacks; fault attacks; post-quantum cryptography; public key encryption and protocols; cryptographic constructions; blockchains.
60 Days to LinkedIn Mastery
There's only one place in the world where you can find and connect with hundreds of millions of professionals every day, and that's on LinkedIn. Are you taking advantage of it? Or are you who Gary Vaynerchuk is talking about when he says, "So many . . . are missing out on the insane opportunity on LinkedIn right now."Tragically, too many of the almost 800 million people on LinkedIn are missing out because they use it the wrong way, but that spells opportunity for those who use it correctly. The good news is, with this book as your guide, you'll be an expert LinkedIn user in no time.Whether you're an employee who dreams of finding a new job, an executive who needs to hire star talent, or an entrepreneur who wants to grow a business, LinkedIn Mastery is the super-simple, straightforward, practical blueprint that will help you achieve your goals.This step-by-step guide to mastering LinkedIn will teach you how to: Optimize your LinkedIn profile so it's something you're proud to show off, rather than something you want to hideMake high-quality connections on LinkedIn with your ideal audience-the people you can serve and who can serve youCreate compelling content-quickly, easily, and affordably-that will bring your dream opportunities to youThis book contains 60 LinkedIn lessons, each short enough to understand and implement in 15 minutes or less. If you complete one each day, within 60 days you'll fully master LinkedIn. If you're looking to find a new job, your LinkedIn profile will attract the best employers and the best offers. If you're recruiting, you'll find and connect with top talent. And if you're generating leads and growing your business, you'll create content that brings your ideal customer to you.Are you ready for your first lesson?
Navigating Hyperspace
Like a hurricane that exposes the underlying bedrock--and an occasional hidden treasure--by washing away the accumulated grains of sand, the pandemic blew away the accumulated certainties and securities of the globally connected, digitized society. Suddenly, nothing can be taken for granted: visiting ailing relatives, shopping--or going to church. The internet and, particularly, social networking sites have become the indispensable infrastructure holding our sociability together. The global companies of the digital economy profited handsomely. How about the users of their services? This volume explores how priests inhabit the digital environment of social networking sites, specifically Facebook. The authors looked at how they present themselves, what they publish, and how people engage with this content. The context of the pandemic suggested that we should also examine how digital technology and social media are being used for purposes of priestly ministry. Our hope is that these analyses and considerations will help not just priests but every person at becoming proficient not only in things virtual but also in practicing virtue.
Cryptology and Network Security
This book constitutes the refereed proceedings of the 20th International Conference on Cryptology and Network Security, CANS 2021, which was held during December 13-15, 2021. The conference was originally planned to take place in Vienna, Austria, and changed to an online event due to the COVID-19 pandemic.The 25 full and 3 short papers presented in these proceedings were carefully reviewed and selected from 85 submissions. They were organized in topical sections as follows: Encryption; signatures; cryptographic schemes and protocols; attacks and counter-measures; and attestation and verification.
Bulletproof TLS and PKI, Second Edition
Bulletproof TLS and PKI is a complete guide to using TLS encryption and PKI to deploy secure servers and web applications. Written by Ivan Ristic, author of the popular SSL Labs web site, this book will teach you everything you need to know to protect your systems from eavesdropping and impersonation attacks.In this book, you'll find just the right mix of theory, protocol detail, vulnerability and weakness information, and deployment advice to get your job done: Comprehensive coverage of the ever-changing field of SSL/TLS and Internet PKI, with updates to the digital versionFor IT professionals, help to understand security risksFor system administrators, help to deploy systems securelyFor developers, help to secure web applicationsPractical and concise, with added depth as neededIntroduction to cryptography and the Internet threat modelCoverage of TLS 1.3 as well as earlier protocol versionsDiscussion of weaknesses at every level, covering implementation issues, HTTP and browser problems, and protocol vulnerabilitiesCoverage of the latest attacks, such as BEAST, CRIME, BREACH, Lucky 13, RC4 biases, Triple Handshake Attack, and HeartbleedThorough deployment advice, including advanced technologies, such as Strict Transport Security, Content Security Policy, and pinningGuide to using OpenSSL to generate keys and certificates and to create and run a private certification authorityGuide to using OpenSSL to test servers for vulnerabilitiesThis book is also available in a variety of digital formats directly from the publisher. Visit us at www.feistyduck.com.
CISSP Examination Review Guide
- The SEMAIS CISSP study guide aims to help testing candidates synthesize and summarize relevant CISSP information. Therefore, a certification candidate might think of this study guide as a mini CISSP examination.- It is especially useful for difficult or complex IT Security concepts or subject areas.- The primary advantage of using this guide is that it organize the amount of information to be learned. Also, learning is improved through applying the 8-domain knowledge to real-time IT Security experience.- A certification candidate will grasp several concepts related to the CISSP 8 domains for driving IT Security best practices and industry standards in this guide.- A candidate may use more than one organizing strategy when assessing questions in this study guide.- Remember, PROFICIENCY in a SMALLER amount of information is your goal.
Securing 5g and Evolving Architectures
SECURING and EVOLVING ARCHITECTURES 5G initiates a period of technological evolution where the benefits transcend faster data download speeds and enable services that will change the way we all live and consume technology. Leveraging 5G's openness, a new developer ecosystem is building breakthrough services that billions of people will consume, delivering immense value to enterprises and subscribers alike. For 5G to achieve its potential, organizations must embrace multi-layered security that goes far beyond 3GPP specifications. Now, leading security architect Pramod Nair helps network professionals climb the steep learning curve associated with securing 5G, fully understand its threat surfaces, systematically mitigate its risks, and maximize the value of their security investments. This coherent, pragmatic, and vendor-agnostic guide will help you plan for security from the outset, make better choices throughout the lifecycle, and develop the mindset needed to secure new generations of networks. You'll find all you need: from high-level 5G security concepts to in-depth coverage of specific security controls, end-to-end architectural guidance, 5G security use cases, and cutting-edge "quantum proofing." Throughout, practical examples and real-life scenarios help you apply Nair's insights---whether you're a service provider, an enterprise, an industry vertical, a startup, a cybersecurity vendor, a systems integrator, or even in a defense environment. Securing 5G and Evolving Architectures is for technical and management audiences at all levels of 5G experience---from enterprise and security architects to network engineers, cloud computing and data center professionals, to CSO and CTO teams. Explore new 5G security challenges---and why you still need external controls, even with recent 3GPP improvements Implement network component security controls for RAN, Transport, 5GC, and devices Safeguard Multi-Access Edge Compute (MEC), SDNs, virtualized 5G cores, and massive IOT Protect Public and Non-Public Networks (Private 5G) deployment scenarios Secure Critical Infrastructure, Vehicle to Everything (V2X), and Smart Factory use cases Optimize end-to-end 5G security architecture across all 5G domains based on zero trust Prioritize 5G security investments in service provider or enterprise environments Preview emerging 5G use cases and ML/AI-based security enhancements
Security and Trust Management
This book constitutes the proceedings of the 17th International Workshop on Security and Trust Management, STM 2021, co-located with the 26th European Symposium on Research in Computer Security, ESORICS 2021. The conference was planned to take place in Darmstadt, Germany. It was held online on October 8, 2021, due to the COVID-19 pandemic.The 10 papers presented in this volume were carefully reviewed and selected from 26 submissions. They were organized in topical sections on applied cryptography; privacy; formal methods for security and trust; and systems security.
Information Systems Security
This book constitutes the proceedings of the 17th International Conference on Information Systems Security, ICISS 2021, held in Patna, India, during December 16-20, 2021. The 9 regular papers, 2 short papers and 4 work-in-progress papers included in this volume were carefully reviewed and selected from a total of 48 submissions. The papers were organized in topical sections named: attack detection, malware identification, data security in distributed systems, and applied cryptography.
Advances in Cryptology - ASIACRYPT 2021
The four-volume proceedings LNCS 13090, 13091, 13092, and 13093 constitutes the proceedings of the 27th International Conference on the Theory and Application of Cryptology and Information Security, ASIACRYPT 2021, which was held during December 6-10, 2021. The conference was planned to take place in Singapore, but changed to an online format due to the COVID-19 pandemic. The total of 95 full papers presented in these proceedings was carefully reviewed and selected from 341 submissions. The papers were organized in topical sections as follows: Part I: Best paper awards; public-key cryptanalysis; symmetric key cryptanalysis; quantum security; Part II: physical attacks, leakage and countermeasures; multiparty computation; enhanced public-key encryption and time-lock puzzles; real-world protocols; Part III: NIZK and SNARKs; theory; symmetric-key constructions; homomorphic encryption and encrypted search; Part IV: Lattice cryptanalysis; post-quantum cryptography; advanced encryption and signatures; zero-knowledge proofs, threshold and multi-signatures; authenticated key exchange.
Beginning React and Firebase
Use React with Firebase to build four beginner-friendly apps. A lot of React tutorials out there today only cover basic web apps, but with additional features the web apps included in this book can be converted into fully scaled startups. You will start with the basics: learn to deploy a React app with Firebase hosting. Next, you will learn to create a fully functional "ToDo" app that will use Firebase database to store a list action items. You will also learn to create a "Stories" app, in which you can show short vertical videos, and a document storage app. Here, we will be able to log in using Google Authentication, and will learn to store files in the app using Firebase storage. Lastly, you will create a career social media app. Your users will be able to log in using email and password authentication. You will learn to use Redux in this project.While creating these web apps, you will employ multiple concepts, including React hooks, React components, and how to use Material UI. You will learn to use Firebase to host your database, as well as hosting your app. With these projects in your portfolio you'll be ready to take your developer skills to the next level. What You'll Learn Use Firebase's powerful services, and how to connect Firebase with ReactExplore the React ecosystem, including Redux and React hooksWork with MaterialUI, the popular React UI frameworkUnderstand how to use Google Authentication techniques in your sitesDeploy all sites using simple Firebase hosting Who This Book Is For Developers at the beginning of their career, or anyone who wants to take their React skills to the next level.
Software Design Patterns for Java Developers
PracticeDesign Patterns to Enrich and Streamline Software DevelopmentKey FeaturesClassify design patterns into three broad categories.Deep dive into design patterns with individual chapters covering them in detail.Understand design patterns to fast track and streamline the development effort.Description'Software Design Patterns for Java Developers' discusses the fundamentals of software design as well as well-established design patterns that simplify and outperform the entire software development cycle.To begin with, the book covers the various types of software design patterns and how they differ from one another. Using numerous examples, you can investigate the implementation of various design patterns such as singleton, object pool, adapter, abstract factory, and proxy. Other design patterns include simplifying complex systems, changing the algorithm behavior in runtime, securing broadcasting messages, and many more. Additionally, a chapter is dedicated to understanding some of the most effective design principles and anti-patterns available today.Throughout the book, you will implement the design patterns and understand their purpose, benefits, potential drawbacks, and challenges for each of these design patterns.What you will learnProvide design solutions that are clean and transparent.Design low maintenance and low cost systems.Design reusable and scalable solutions. Design solutions that are easy to understand and readable.Utilize time-tested and continually refined design best practises.Avoid pitfalls during the course of designing a system.Who this book is forThis book is for software developers, experienced programmers, software architects with basic understanding of software development and are comfortable working with medium to large-scale systems. Best to have hands on experience with Java programming in order to read this book.Table of Contents1. Enlighten Yourself2. One of a Kind3. Object Factory4. Delegate Object Construction5. Recycle and Reuse6. Adapter7. Decorating Objects8. The Guardian9. Simplifying the Complexity10. Template11. Keep a close eye12. State and behaviours13. Executing Commands14. Beyond Design PatternsRead more
Webflow by Example
Build modern responsive websites without writing code by making the most of the power and flexibility of WebflowKey Features: Get to grips with Webflow to build and launch responsive websites from scratchLearn how to put Webflow into practice and take advantage of its power and flexibilityBuild your own modern responsive websites from scratch and without any code Book Description: Webflow is a modern no-code website-builder that enables you to rapidly design and build production-scale responsive websites. Webflow by Example is a practical, project-based, and beginner-friendly guide to understanding and using Webflow to efficiently build and launch responsive websites from scratch.Complete with hands-on tutorials, projects, and self-assessment questions, this easy-to-follow guide will take you through modern web development principles and help you to apply them efficiently using Webflow. You'll also get to grips with modern responsive web development and understand how to take advantage of the power and flexibility of Webflow. The book will guide you through a real-life project where you will build a fully responsive and dynamic website from scratch. You will learn how to add animations and interactions, customize experiences for users, and more. Finally, the book covers important steps and best practices for making your website ready for production, including SEO optimization and how to publish and package the website.By the end of this Webflow book, you will have gained the skills you need to build modern responsive websites from scratch without any code.What You Will Learn: Build and customize websites without any codeUnderstand how to approach designing and developing for the modern webBecome familiar with the main functionalities of WebflowFollow best practices for Webflow development while working on a practical project, from its design to launchHarness the power of the Webflow CMS to create dynamic contentAdd modern flourishes to a website using pre-defined and custom animations and interactionsWho this book is for: If you're an entrepreneur, web designer, or anyone with little web development knowledge, this book will help you learn how to build fully responsive websites and web prototypes without writing a single line of code. If you're a web designer, this book will make you a more informed web developer. If you're already a developer, this book will help you become a better web designer.
Microsoft Sentinel in Action - Second Edition
Learn how to set up, configure, and use Microsoft Sentinel to provide security incident and event management services for your multi-cloud environmentKey Features: Collect, normalize, and analyze security information from multiple data sourcesIntegrate AI, machine learning, built-in and custom threat analyses, and automation to build optimal security solutionsDetect and investigate possible security breaches to tackle complex and advanced cyber threats Book Description: Microsoft Sentinel is a security information and event management (SIEM) tool developed by Microsoft that helps you to integrate cloud security and artificial intelligence (AI). This book will enable you to implement Microsoft Sentinel and understand how it can help detect security incidents in your environment with integrated AI, threat analysis, and built-in and community-driven logic.The book begins by introducing you to Microsoft Sentinel and Log Analytics. You'll then get to grips with data collection and management, before learning how to create effective Microsoft Sentinel queries to detect anomalous behaviors and activity patterns. Moving ahead, you'll learn about useful features such as entity behavior analytics and Microsoft Sentinel playbooks along with exploring the new bi-directional connector for ServiceNow. As you progress, you'll find out how to develop solutions that automate responses needed to handle security incidents. Finally, you'll grasp the latest developments in security, discover techniques to enhance your cloud security architecture, and explore how you can contribute to the security community.By the end of this Microsoft Sentinel book, you'll have learned how to implement Microsoft Sentinel to fit your needs and be able to protect your environment from cyber threats and other security issues.What You Will Learn: Implement Log Analytics and enable Microsoft Sentinel and data ingestion from multiple sourcesGet to grips with coding using the Kusto Query Language (KQL)Discover how to carry out threat hunting activities in Microsoft SentinelConnect Microsoft Sentinel to ServiceNow for automated ticketingFind out how to detect threats and create automated responses for immediate resolutionUse triggers and actions with Microsoft Sentinel playbooks to perform automationsWho this book is for: If you are an IT professional with prior experience in other Microsoft security products and Azure and are now looking to expand your knowledge to incorporate Microsoft Sentinel, then this book is for you. Security experts using an alternative SIEM tool who want to adopt Microsoft Sentinel as an additional service or as a replacement will also find this book useful.
Computational Analysis of Storylines
Event structures are central in Linguistics and Artificial Intelligence research: people can easily refer to changes in the world, identify their participants, distinguish relevant information, and have expectations of what can happen next. Part of this process is based on mechanisms similar to narratives, which are at the heart of information sharing. But it remains difficult to automatically detect events or automatically construct stories from such event representations. This book explores how to handle today's massive news streams and provides multidimensional, multimodal, and distributed approaches, like automated deep learning, to capture events and narrative structures involved in a 'story'. This overview of the current state-of-the-art on event extraction, temporal and casual relations, and storyline extraction aims to establish a new multidisciplinary research community with a common terminology and research agenda. Graduate students and researchers in natural language processing, computational linguistics, and media studies will benefit from this book.
Spring REST
Design and develop Java-based RESTful APIs using the latest versions of the Spring MVC and Spring Boot frameworks. This book walks you through the process of designing and building a REST application while delving into design principles and best practices for versioning, security, documentation, error handling, paging, and sorting. Spring REST provides a brief introduction to REST, HTTP, and web infrastructure. You will learn about several Spring projects such as Spring Boot, Spring MVC, Spring Data JPA, and Spring Security, and the role they play in simplifying REST application development. You will learn how to build clients that consume REST services. Finally, you will learn how to use the Spring MVC test framework to unit test and integration test your REST API. After reading this book, you will come away with all the skills to build sophisticated REST applications using Spring technologies. What You Will LearnBuild Java-based microservices, native cloud, or any applications using Spring RESTEmploy Spring MVC and RESTful SpringBuild a QuickPoll application exampleDocument REST services, as well as versioning, paging, and sortingTest, handle errors and secure your application Who This Book Is For Intermediate Java programmers with at least some prior experience with Spring and web/cloud application development.
Myths Vs. Facts Of Cryptocurrency
Myths Vs. Facts Of Cryptocurrency - A Beginner's Guide To Understanding Cryptocurrencies & Blockchain TechnologyThe birth of Bitcoin in 2009 gave rise to a new worldwide and unrestricted currency and movement that wouldn't fully be recognized until ten years later. With over 10,000 digital currencies and altcoins at the writing of this, it's key to understand what cryptocurrency and blockchain technology are so you know where we're headed for the future and you can be informed accordingly.Whether you want to invest into crypto or you're seeking more knowledge because it's all you can hear about these days, this book will provide valuable insights. If you do any cursory search you'll find the topic of cryptocurrency is littered with reports of fraudulent scams and illegal activity. Many will even claim it's volatile and extremely risky, and to "avoid at all costs."However, the goal of this book is not to serve as an investment guide or financial advice, but rather, to educate beginners and those just getting into the investment and technology space of cryptocurrency so they know what to look for, what to avoid, and how to make a sound decision regardless of what investment you choose. Cryptocurrency is not illegal, but there are many who will exploit the ignorant for their personal gain. Despite these situations, more and more financial, governmental, business, and investor entities are getting involved with crypto. This sheds light on the powerful utility of cryptocurrency beyond its mere monetary value for selling and buying goods. It goes well beyond that and could pave the way for an exciting new future as we shift to Web 3.0.In Myths Vs. Facts Of Cryptocurrency, you will discover: -The Birth of Cryptocurrency-A Snapshot Into The World Of Cryptocurrency-Terms & Definitions of Cryptocurrency-The Value of Cryptocurrency-Cryptocurrencies Versus Physical (Fiat) Currencies: What You Should Know-Cryptocurrency Versus the Financial Market-The Relevance of Cryptocurrencies & Industries-Top Myths & Hard Facts About Cryptocurrencies-Mindful Investing In Cryptocurrency-Blockchain & Cryptocurrencies-Thoughts On Crypto's Utility: To Use Or Not To UseI do not want you to fall victim to fraudulent schemes due to naivety or lack of appropriate information or research before delving into the world of cryptocurrency. My hope is that this book will serve as your starting block, a guide into what cryptocurrency is and what it isn't. The future is a bright one and full of opportunities when you plan and possess the necessary information and trust to make sound decisions and choices.
The Next Floor
This is a story about how 185 residents of a newly commissioned, multi-story Village Apartments in a suburb of Canberra, Australia, constrain both villains and the Covid-19 pandemic from destroying their retirement. The Security Response Committee (SRC) of 8 senior citizens headed by an 84 year old German emerges as the paramount authority, leading residents safely through to a post-apocalyptic future none thought was possible.
Blockchain and Trustworthy Systems
This book constitutes the thoroughly refereed post conference papers of the Third International Conference on Blockchain and Trustworthy Systems, Blocksys 2021, held in Guangzhou, China, in August 2021.*The 38 full papers and the 12 short papers were carefully reviewed and selected from 98 submissions. The papers are organized in topical sections: Contents Blockchain and Data Mining; Performance Optimization of Blockchain; Blockchain Security and Privacy; Theories and Algorithms for Blockchain; Blockchain and Internet of Things; Blockchain and Smart Contracts; Blockchain Services and Applications; Trustworthy System Development.*
Certified Information Security Manager Exam Prep Guide
Pass the Certified Information Security Manager (CISM) exam and implement your organization's security strategy with easeKey Features: Pass the CISM exam confidently with this step-by-step guideExplore practical solutions that validate your knowledge and expertise in managing enterprise information security teamsEnhance your cybersecurity skills with practice questions and mock tests Book Description: With cyber threats on the rise, IT professionals are now choosing cybersecurity as the next step to boost their career, and holding the relevant certification can prove to be a game-changer in this competitive market. CISM is one of the top-paying and most sought-after certifications by employers.This CISM Certification Guide comprises comprehensive self-study exam content for those who want to achieve CISM certification on the first attempt. This book is a great resource for information security leaders with a pragmatic approach to challenges related to real-world case scenarios. You'll learn about the practical aspects of information security governance and information security risk management. As you advance through the chapters, you'll get to grips with information security program development and management. The book will also help you to gain a clear understanding of the procedural aspects of information security incident management.By the end of this CISM exam book, you'll have covered everything needed to pass the CISM certification exam and have a handy, on-the-job desktop reference guide.What You Will Learn: Understand core exam objectives to pass the CISM exam with confidenceCreate and manage your organization's information security policies and procedures with easeBroaden your knowledge of the organization's security strategy designingManage information risk to an acceptable level based on risk appetite in order to meet organizational goals and objectivesFind out how to monitor and control incident management proceduresDiscover how to monitor activity relating to data classification and data accessWho this book is for: If you are an aspiring information security manager, IT auditor, chief information security officer (CISO), or risk management professional who wants to achieve certification in information security, then this book is for you. A minimum of two years' experience in the field of information technology is needed to make the most of this book. Experience in IT audit, information security, or related fields will be helpful.
Risk Control Theory of Online Transactions
Online transaction has become an important part of the new economy and finance. At the same time, transaction payment fraud also presents an explosive trend.This unique compendium introduces risk control theories technologies of online transaction processes, and applies the traditional security technologies and advanced behavior authentication methods to the trustworthy guarantee of online transaction systems. The comprehensive volume also promotes the development of trustworthy online transaction theory and technologies.This useful reference text will benefit researchers in the field of computer science and technologies, as well as a research reference in the field of online transaction risk prevention and control.
Information Security
This book constitutes the proceedings of the 24rd International Conference on Information Security, ISC 2021, held virtually, in November 2021. The 21 full papers presented in this volume were carefully reviewed and selected from 87 submissions. The papers categorized into the following topical subheadings: cryptology; web and OS security; network security; detection of malware, attacks and vulnerabilities; and machine learning for security.
PHP/Architect's Guide to Date and Time Programming
If your development involves working with dates and times, then this book is a must-have. In this book, Derick Rethans (contributor to PHP's core date extension and well-known PHP expert) explores in great detail the subtle nuances of working with dates and times. Frequently PHP developers encounter unexpected results that adversely affect their software and web applications. This book will undoubtedly help them tackle those issues. This book covers a variety of areas including: history of calendars and time standards, giving the reader a better understanding of how date/time concepts evolved into the way they are today parsing date/time strings and the potential pitfalls a developer can encounter timezones, the quirks inherent in them, and how your application can handle these quirks formatting and representing times and dates correctly and dealing with the DateTime Object manipulating and working with past, future and recurring dates obtaining dates when timestamps aren't available format specifiers upgrading the master timezone database What are PHP experts saying about this book? "Complex date and time programming isn't just for international applications. Even in the US, we have to deal with up to nine different time zones, and shifting between these can be difficult. Derick is one of the most knowledgeable people I know when it comes to date and time programming. I have turned to him countless times for help, and now he brings that depth of knowledge to this book. If you need to parse dates and times, shift between time zones, or manipulate dates and times in your applications then this book is for you." - Ben Ramsey "If you ever have to deal with parsing or formatting timestamps, or dealing with timezones this is the definite reference to make your time related PHP coding tasks fast and simple!" -Elizabeth Marie Smith This is the most comprehensive book on date/time data for PHP available, and one that any PHP developer can't do without.
Cisco Data Center Fundamentals
Get ready to configure and operate modern data centers--and move up to high-value CCNP Data Center (DC) certification Cisco Data Center Fundamentals is the complete guide for network engineers and other professionals who need a solid understanding of modern data center technologies. Especially useful for those preparing for the Cisco DCCOR exam and Cisco Certified Network Professional (CCNP) Data Center certification, it fully addresses the essentials of networking, storage, compute, and automation in today's data center environments. Authored by two long-time experts in operating Cisco data centers and developing official Learning@Cisco training for them, this guide explains each concept step by step, balancing depth and breadth, and maximizing clarity throughout. The authors go far beyond introducing relevant products, protocols, and features. They illuminate underlying technologies, identify key interdependencies, walk through configuring working solutions, and truly help prepare you to set up and operate a modern data center. Gain a holistic, unified understanding of the data center and its core components Walk through installation and deployment of key data center technologies Explore potential applications to see what's possible in your environment Learn how Cisco switches and software implement data center networking and virtualization Discover and apply data center network design and security best practices Review Cisco data center storage technologies and concepts, including Fibre Channel, VSANs, storage virtualization, and FCoE Explore the building blocks of the Cisco UCS data center compute solution, and how UCS uses hardware abstraction and server virtualization Use automation and APIs to improve data center productivity and agility Create and customize scripts for rapid troubleshooting Understand cloud computing for the data center: services, deployment models, and the Cisco Intersight hybrid cloud operations platform
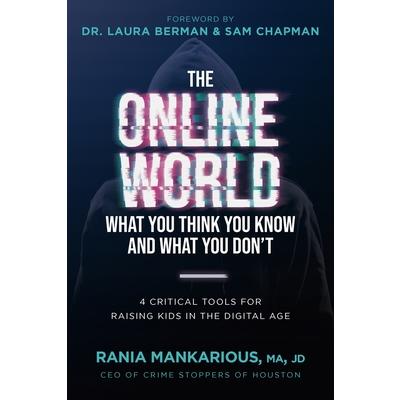
The Online World, What You Think You Know and What You Don't
Every Child Who Has Access to a Smartphone, Tablet, Computer, or Video Games is at Risk!But NOW You Can Help Keep Them Safe.Would you ever consider putting your child on a plane and sending them to a foreign country alone? Of course, you wouldn't. And while that seems like an extreme example...guess what, mom and dad-that's exactly what you do when you hand your child a device without preparation. There are hundreds of millions of users on any given platform on any given day. Suffice it to say, when you give your child access to the online world, you give the world access to your child."The most dangerous neighborhood for your child to be in is in your own house, online."National Center on Sexually Exploited ChildrenAside from the half-million predators targeting millions upon millions of kids each day, drug dealers, pornography, sextortion, cyberbullying, gaming addiction are all threats to our children. While most experts agree that you should just keep your kids off the internet, in today's world, that's almost impossible.Technology will find it's way into your child's life and so parents, we must prepare our children for this world so we can keep them healthy and safe.Finally--A Solution Parents Love That Kids Can Live With!This is the first book with a plan designed to keep kids safe anywhere they go online! In "The Online World: What You Think You Know and What You Don't" Rania Mankarious, Public Safety Expert and CEO of Crime Stoppers Houston, pulls back the curtain to the online world and helps parents take all the intangible gray space that can seem so overwhelming, and turn it into defined territories with boundaries to protect our tweens and teens. In this book, Rania shares her 4-Tool Strategy that will guide you and your child through real discussions about how to safely navigate the online world. Tool #1 Will: Define with clarity your child's purpose for being online and how they will portray themselves to the online community. Tool #2 Will: Pull back the curtain on who really is in your child's online community, and how to recognize the three red flags everyone should be aware of.Tool #3 Will: Make your child aware of the many internal and external dangers of the online world, and develop an exit strategy so they are prepared when a threat comes their way.Tool #4 Will: Teach your child what it means to post safely-and give them a framework they will be excited to follow!What Rania has discovered is that if we focus on these four areas, and empower our kids with knowledge and strategy, we can address ALL the possible areas of online concern for parents. Best of all, these solutions will stand over time, regardless of how the landscape of the online world changes. Order your copy today and protect the kids you love!